Vpns Proxies And Zscaler Whats The Difference And Do You Need Them: A Deep Dive For VPNs, Proxies, And Enterprise Security
Vpns proxies and zscaler whats the difference and do you need them? Quick fact: Vpns, proxies, and Zscaler all help you stay safer online, but they serve different purposes and fit different situations. In this video-ready guide, you’ll get a clear, practical breakdown of what each tech actually does, when to use it, and how they stack up in real life. Below is a comprehensive, user-friendly overview designed for learners, IT folks, and everyday users who want solid, actionable guidance.
Useful quick take
- If you just need to browse securely on public Wi‑Fi, a consumer VPN is often enough.
- If you’re managing a business network and need centralized policy control, Zscaler offers enterprise-grade security as a service.
- Proxies are great for lightweight tasks like hiding IPs for casual browsing or specific testing, but they won’t protect you from malware like a VPN or a modern security platform.
What you’ll learn in this guide Tiktok not working in china even with a vpn heres the real reason
- The core differences between VPNs, proxies, and Zscaler
- When to choose a VPN vs a proxy vs Zscaler
- How they work at a technical level in plain language
- Real-world use cases and examples
- Pros, cons, pricing ranges, and typical performance implications
- A practical checklist to decide what you need
- A handy FAQ with practical answers
Introduction: Quick overview and why this matters Vpns proxies and zscaler whats the difference and do you need them? Here’s the bottom line: you’ll likely encounter all three at some point, and each serves a different purpose in your online safety, privacy, and network management toolbox. Think of it like this: a VPN creates a secure tunnel to protect you and your data; a proxy acts as a relay to fetch content on your behalf; Zscaler is a cloud-delivered security stack that enforces policies, inspects traffic, and blocks threats at scale. Depending on your needs—personal privacy, bypassing regional blocks, or enterprise-grade protection—you’ll pick one, or a combination.
In this guide you’ll find:
- Plain-language explanations
- Real-world examples you can relate to
- Side-by-side comparisons to help you decide quickly
- Practical steps to implement and test
- A curated list of resources to deepen your understanding
Useful URLs and Resources text only Apple Website - apple.com, Wikipedia - en.wikipedia.org, Microsoft Defender - microsoft.com, Cloudflare Privacy - blog.cloudflare.com, Zscaler Official - zscaler.com, NordVPN Official - nordvpn.com, ProtonVPN Official - protonvpn.com, Tor Project - www.torproject.org, WhatIsMyIP - whatismyipaddress.com, TechRadar VPN Guide - www.techradar.com/vpn
What’s a VPN, exactly?
- Definition: A VPN Virtual Private Network creates a secure, encrypted tunnel between your device and a VPN server. Your internet traffic travels through that server, masking your IP address and encrypting data in transit.
- Core benefits:
- Privacy from your ISP and local network observers
- Encryption on public networks hotels, cafes, airports
- Ability to appear as if you’re in another country to access geo-restricted content
- Limits:
- Not all VPNs are equally private; some log data
- Performance can drop due to encryption and the distance to the VPN server
- Does not automatically protect you from malware or phishing unless paired with additional security tools
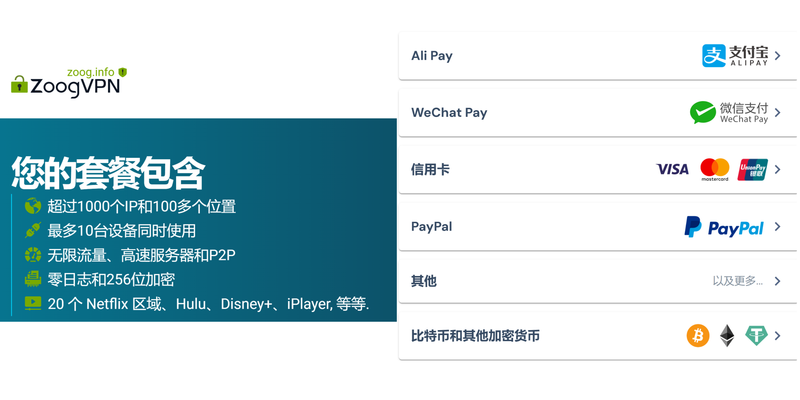
What’s a proxy, exactly? Nordvpn browser extension for microsoft edge a comprehensive guide for 2026
- Definition: A proxy acts as an intermediary for requests from clients seeking resources from other servers. It fetches the content on your behalf and returns it to you.
- Core benefits:
- Simple IP masking for specific tasks
- Useful for testing or scraping where you don’t need full device encryption
- Often easier and cheaper for light use
- Limits:
- Proxies often don’t encrypt traffic
- Many proxies don’t protect against malware or malicious sites
- They can be detected and blocked by some services
- Not a comprehensive security solution
What is Zscaler?
- Definition: Zscaler is a cloud-based security platform that provides secure access to the internet and private apps. It operates as a service, enforcing policies across users and devices regardless of location.
- Core benefits:
- Centralized security controls for organizations
- Threat prevention, data loss prevention, and access control
- Scalable, easy to roll out for many users
- SSL inspection, sandboxing, URL filtering, and more
- Limits:
- Primarily aimed at enterprises; consumer-grade usage is not the target
- Requires proper policy configuration; misconfigurations can hinder productivity
- Privacy concerns can arise due to traffic inspection in enterprise contexts
Key differences summarized
- VPN: Encrypts all traffic from your device to a VPN server; creates a secure tunnel; hides your IP; can access geo-blocked content; depends on the VPN provider’s security and logging policy.
- Proxy: Relays your traffic to fetch content; can mask your IP for specific tasks; not encryption-heavy by default; often used for content access or testing.
- Zscaler: Enterprise security service; inspects and enforces policies on traffic; protects against threats, enforces access rules, and secures cloud apps; not a consumer VPN but a security platform.
Common use cases by scenario
- Personal privacy on public Wi‑Fi
- Best option: VPN with a strong no-logs policy and robust encryption
- Why: It protects data in transit and hides your IP from local observers
- Bypassing geographic restrictions for streaming or browsing
- Best option: VPNs with servers in the target region
- Why: Access content as if you’re there, but be mindful of terms of service
- Lightweight content testing or data collection
- Best option: Proxies HTTP/HTTPS proxies or VPNs if you need encryption
- Why: Proxies can be faster for certain tasks; security may be lower
- Enterprise security and policy enforcement
- Best option: Zscaler or similar SASE/secure web gateway solutions
- Why: Centralized protection, policy enforcement, threat intelligence, and scalable management
- Remote work with sensitive data
- Best option: VPN plus enterprise security tools; consider a corporate-approved VPN and Zscaler for cloud access
- Why: You get privacy, encryption, and policy-driven protection
Technical differences you’ll notice in practice
- Encryption and protocol:
- VPNs: Use protocols like OpenVPN, WireGuard, IKEv2/IPsec. Strong encryption AES-256 often is common.
- Proxies: Usually don’t encrypt traffic unless you’re using a secure proxy HTTPS proxy; not designed for end-to-end security.
- Zscaler: Encrypts and inspects traffic as it passes through the cloud security stack; SSL inspection may occur, which requires proper certificate handling.
- Traffic visibility:
- VPNs: You see encrypted traffic to the VPN server; the VPN provider can see metadata unless you use features like split tunneling with careful configuration.
- Proxies: The proxy sees your requests and content; you generally control which traffic goes through the proxy.
- Zscaler: The security backbone inspects traffic to enforce policies, block threats, and enforce data loss prevention; users don’t usually see all the inspection details.
- Scope:
- VPNs: Device-wide coverage depends on configuration for all apps traffic.
- Proxies: Per-application or per-request basis; can be configured per browser or system-level, but not universally across all apps unless you route all traffic.
- Zscaler: Enterprise-wide, with policies centralized in the cloud; supports VPN-like secure access plus secure web gateway features.
Real-world numbers and data to consider Softether vpn download 최신 버전 설치부터 활용까지 완벽 가이드: VPNs 카테고리의 심화 가이드와 활용 팁
- Privacy and logs:
- Many consumer VPNs offer “no-logs” policies, but you should read the privacy policy and independent audits if available.
- Some VPNs provide transparency reports and third-party audits; check for credible certs and audits.
- Speed considerations:
- VPNs can impact speeds by 10–40% on average, depending on server location, protocol, and network conditions.
- Proxies can be faster for certain tasks but may introduce latency if the proxy server is far away or overloaded.
- Zscaler can add latency due to security processing and SSL inspection, but it’s designed to be scalable and provide consistent protection.
- Security features:
- VPNs: Strong encryption, kill switch, DNS leak protection, split tunneling.
- Proxies: Basic IP masking, usually no encryption, some proxies offer SOCKS5 or HTTPS variants with varying levels of anonymity.
- Zscaler: Threat protection, malware defense, URL filtering, data loss prevention, identity-based access control, secure access to SaaS and private apps.
Formats you’ll find useful for comprehension
- Quick comparison table text version
- VPN: Encrypts all traffic, masks IP, broad protection, potential speed impact, consumer-grade or business options
- Proxy: Subset traffic, masks IP for specific tasks, usually no encryption, lighter protection
- Zscaler: Cloud-based security and policy enforcement, enterprise-grade, extensive threat protection, SSL inspection
- Step-by-step decision guide
- Do you need encryption for all traffic on all apps? Yes → VPN
- Do you only need to hide your IP for a specific task or app? Yes → Proxy
- Are you an organization needing centralized threat prevention and policy control? Yes → Zscaler or similar SASE
- Do you require access to private apps and secure web access for remote workers? Yes → Evaluate VPN + Zscaler integration
- Use-case checklist
- Personal privacy on public networks: VPN with reputable provider
- Geo-unblocking for streaming: VPN in a country with a good server base for streaming
- Light content testing: Proxy for speed, but verify security needs
- Enterprise security: Zscaler for cloud security, threat protection, policy enforcement
- Compliance and data protection: VPN + Zscaler with proper data handling and logging policies
Common myths debunked
- Myth: A VPN makes you completely anonymous.
- Reality: It hides your IP and encrypts traffic, but it doesn’t make you completely anonymous. Provider logs, account behavior, and browser fingerprints can still reveal information.
- Myth: Proxies are the same as VPNs.
- Reality: Proxies route traffic but typically don’t encrypt it. VPNs provide full-device encryption and tunnel protection.
- Myth: Zscaler is just a VPN.
- Reality: Zscaler is a security platform that includes secure web gateway, zero trust networking, and threat prevention, not merely a VPN.
Implementation tips practical steps
- Choosing a VPN
- Look for a no-logs policy, independent audits, strong encryption AES-256, modern protocols WireGuard or OpenVPN, reputable jurisdiction, good customer reviews, and transparent privacy practices.
- Check server coverage: Do they have servers in the locations you need? Are speeds adequate?
- Features to consider: Kill switch, DNS leak protection, split tunneling, multi-hop, and device compatibility.
- Using a proxy safely
- Prefer HTTPS proxies for any content that requires encryption. Be cautious about sensitive data transmitted via proxies.
- Use proxies for non-sensitive tasks and testing; avoid entering private credentials through proxies unless you trust the service.
- Implementing Zscaler in an organization
- Start with a pilot group to test policy settings and traffic patterns.
- Define clear policies for acceptable use, data inspection, and privacy impact.
- Ensure SSL inspection is compliant with corporate privacy policies and user consent, and manage exceptions where necessary.
- Train users on what the security platform does and what to expect like possible delays during SSL inspection.
Performance optimization tips
- For VPNs
- Choose a server close to your location to minimize latency
- Use WireGuard where available for better speeds
- Enable split tunneling if you only need the VPN for specific apps or destinations
- For proxies
- Use high-quality, fast proxy servers; avoid free proxies with heavy load
- Prefer proxies with low latency to your target services
- For Zscaler
- Properly configure routing and policy exceptions to minimize unnecessary inspection
- Plan bandwidth and hardware capacity to accommodate SSL inspection and threat processing
Security best practices Surfshark vpn very slow heres how to fix it fast: a complete guide to speeding up Surfshark
- Always keep your software updated: VPN apps, browsers, and OS patches reduce vulnerabilities.
- Use strong, unique passwords and enable 2FA where possible.
- Regularly review privacy policies and data handling practices of any service you rely on.
- If you’re in an enterprise, align with your IT team on allowed configurations and reporting.
How to test what you actually need
- Start with a needs assessment:
- Do you need privacy on public networks? VPN.
- Do you need to test or route a single app through a middleman? Proxy.
- Do you need centralized security, policy enforcement, and cloud access for a team? Zscaler.
- Run a small trial for 1–2 weeks:
- Track speeds, reliability, and whether your security needs are met.
- Note any productivity or compatibility impacts.
- Review logs and privacy implications:
- For VPNs, check what data is logged and how that aligns with your privacy expectations.
- For Zscaler, understand what is being inspected and who can access the data.
Technical glossary brief
- AES-256: A strong encryption standard commonly used by VPNs.
- OpenVPN, WireGuard, IKEv2/IPsec: VPN protocols with different trade-offs in speed and security.
- SSL inspection: The process of decrypting and inspecting SSL/TLS traffic for threats.
- SASE: Secure Access Service Edge, a framework combining SD-WAN and security services in the cloud.
- Zero Trust: A security model that requires strict identity verification for every person and device attempting to access resources.
Statistical snapshot contextual
- VPN popularity: Global VPN usage has been growing consistently, with millions of users relying on VPNs for privacy and access to content.
- Enterprise security adoption: More organizations are adopting cloud-delivered security platforms like Zscaler to support remote work and secure cloud access.
- Performance impact: VPNs typically reduce throughput by 10–40% depending on distance, server quality, and protocol; SSL inspection in Zscaler can add latency but improves protection.
Case studies brief
- Case A: A remote-work team used a VPN for device-wide encryption and a centralized firewall model. They saw improved privacy on public networks and consistent access to company resources.
- Case B: An e-commerce company deployed Zscaler to secure web access for remote employees and to inspect traffic to prevent data leaks, resulting in fewer security incidents and better policy enforcement.
- Case C: A student used a lightweight proxy to bypass regional blocks for research content, but encountered blocked sites and limited security, highlighting why proxies aren’t a substitute for VPNs or enterprise security.
Troubleshooting quick-start Is Mullvad VPN Good for China A Deep Dive Into Bypassing The Great Firewall And Beyond
- VPN won’t connect
- Check server availability, credentials, and protocol settings. Try a different server or protocol.
- Proxy not working
- Verify proxy settings in the browser or app, ensure the proxy is online, and check for IP leaks.
- Zscaler blocks legitimate apps
- Review policy exceptions with your IT admin and ensure legitimate traffic is whitelisted or appropriately routed.
What’s the best path for you?
- If you’re a casual user wanting to protect data on public Wi‑Fi and access region-locked content occasionally: VPN is your best bet.
- If you’re a developer or tester needing to route a specific app’s traffic through a middleman: Proxy is a straightforward tool.
- If you’re an organization needing centralized policy control, threat protection, and secure cloud access for many users: Zscaler or a similar enterprise security platform is the go-to.
Frequently Asked Questions
Do VPNs hide my real IP completely?
VPNs hide your IP from the sites you visit, but the VPN provider can see your traffic and may log data depending on their policy. Independent audits and a no-logs claim help, but no system is perfect.
Can proxies replace VPNs for privacy?
Not really. Proxies don’t typically encrypt traffic, so your data can be exposed. They’re useful for specific tasks but not a full privacy solution.
Is Zscaler a VPN?
No. Zscaler is a cloud-based security platform focusing on policy enforcement, threat protection, and secure access to apps. It’s often used alongside VPNs, not as a direct VPN replacement. My ip address and nordvpn everything you need to know: a complete guide to privacy, geo‑spoofing, and speed
Do I need both VPN and Zscaler?
It depends on your needs. Individuals typically don’t need Zscaler, but businesses use Zscaler to secure traffic and enforce policies. Some enterprises use VPNs for secure access and Zscaler for threat protection.
How does SSL inspection work, and should I worry about privacy?
SSL inspection decrypts traffic to inspect it for threats, then re-encrypts it. It’s a privacy trade-off often justified in corporate settings. Users should know what’s being inspected and ensure privacy policies align with regulations.
Are free VPNs safe?
Free VPNs often come with limitations, data caps, and questionable privacy practices. For meaningful privacy and security, a reputable paid VPN is usually a better choice.
How fast will a VPN slow me down?
Speeds vary. Expect some slowdown due to encryption and distance to the VPN server. Using a fast protocol like WireGuard and selecting a nearby server minimizes impact.
Can I use a proxy for streaming video?
Yes, but many streaming services block proxies. A dedicated VPN with servers in the streaming region is typically more reliable. Norton secure vpn keeps turning off heres how to fix it fast
What’s the difference between a VPN and a smart DNS service?
A VPN encrypts and tunnels all traffic, while a smart DNS changes your apparent location for geo-blocked content without encrypting traffic. Security is lower with DNS services.
How do I evaluate VPNs for privacy and security?
Look for:
- Independent audits and transparent privacy policies
- Strong encryption and up-to-date protocols
- Clear data retention and logging practices
- Independent reviews and reputation
- Good performance and server coverage
Final notes
- If you want to take advantage of a strong, trusted option for VPNs, consider a well-reviewed service with clear privacy assurances and robust performance. And if you’re evaluating enterprise needs, Zscaler can deliver scalable security, threat prevention, and policy enforcement across a distributed workforce.
Note: This guide is crafted to be comprehensive and user-friendly, with practical examples, clear guidance, and actionable steps to help you decide whether you need Vpns, proxies, or Zscaler—and how to implement them effectively.
Sources:
Como comprar una suscripcion a nordvpn en colombia planes precios y guia completa 2026 Vpn proxy ovpnspider 무엇이고 어떻게 사용해야 할까요: VPN, 프록시, OVPNSpider 비교와 활용 가이드
Vpn 土耳其节点:土耳其境内外访问、隐私保护与速度优化的实用指南
Hotel wi fi blocking your vpn heres how to fix it fast
Cj vpn 주소 찾는 법과 안전한 vpn 활용 가이드 2026: 빠르고 안전한 CJ VPN 사용법과 최적의 대안
多邻国破解的合法替代方案:使用 VPN 保护隐私、提升学习体验、解锁受限内容的全面指南