Is vpn safe for ifr heres what you need to know: A Practical Guide to VPN Safety, Privacy, and Performance
Is vpn safe for ifr heres what you need to know? Yes, with the right choices and practices you can stay private, secure, and smoothly connected online. Here’s a detailed, note‑worthy guide that breaks down the safety aspects of using a VPN, what to look for, and how to use it responsibly.
Is vpn safe for ifr heres what you need to know: The quick answer is yes, a reputable VPN can significantly boost privacy and security, but not every VPN is created equal. This guide covers the essentials, including safety considerations, real‑world scenarios, and practical steps you can take today. We’ll walk you through:
- Why VPN safety matters for everyday browsing, streaming, work, and travel
- What a safe VPN should and shouldn’t do
- How to verify a VPN’s safety and trustworthiness
- Common myths and misconceptions vs. real risks
- A practical setup checklist and best practices
- Real‑world stats and what they mean for you
Useful quick facts: Nordvpn mit ikev2 auf iOS 18 verbinden: deine schritt fur schritt anleitung
- VPNs can hide your IP address and encrypt traffic on publicWi‑Fi, reducing risk on the go.
- A safe VPN should have a no‑logs policy, strong encryption, transparent privacy policy, and independent audits where possible.
- Some VPNs can leak DNS or WebRTC data; safe use involves enabling protections and choosing trusted providers.
- Always keep your devices updated, use multi‑factor authentication where available, and review app permissions.
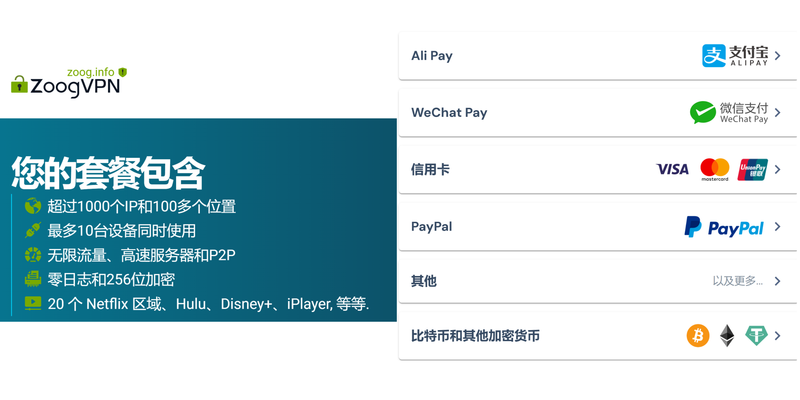
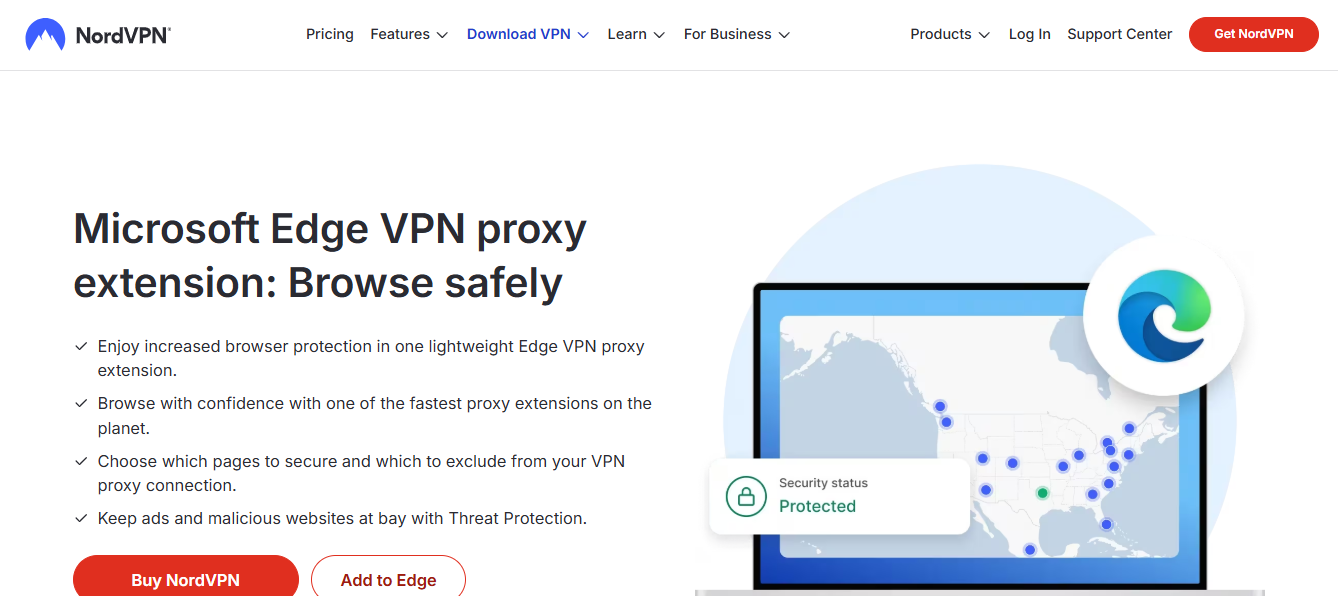
If you’re ready to take control of your online safety, consider a trusted VPN option like NordVPN for privacy and security. For readers who want a quick path to a trusted provider, NordVPN is a popular choice with a long track record and a broad feature set. You can explore options and start your safe browsing journey here: https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441. Text: Safe, Private, Fast VPN — Learn More
Table of Contents
- What makes a VPN safe? Core features to look for
- How VPNs work: encryption, tunneling, and trust
- Safety myths vs. realities
- Real‑world safety: scenarios and best practices
- Privacy and data handling: what to expect from providers
- Security features that matter
- How to test a VPN for safety and leaks
- VPN safety for different devices and networks
- Performance vs. safety: finding the right balance
- Practical setup checklist
- Frequently Asked Questions
What makes a VPN safe? Core features to look for
- Strong encryption: Look for AES‑256 or equivalent and robust key exchange IKEv2/IPsec, OpenVPN, WireGuard.
- No‑logs policy: A clear, verifiable commitment to not log user activity.
- Independent audits: Third‑party assessments of privacy practices and security.
- Transparent privacy policy: Clear explanations of data collection, retention, and usage.
- DNS and WebRTC leak protection: Built‑in protections to prevent leaks that could reveal your true IP.
- Kill switch: Automatically blocks traffic if the VPN connection drops.
- Modern protocols: Preference for WireGuard or OpenVPN with modern configurations for speed and security.
- Jurisdiction: Privacy‑friendly regions with strong data protection laws.
- Independent verification: Public tests showing no traffic leaks and trustworthy practices.
- User controls: Easy‑to‑use settings for privacy, kill switch, and split tunneling.
How VPNs work: encryption, tunneling, and trust
- Encryption: VPNs encrypt your data so ISPs, network admins, or hackers can’t read it easily.
- Tunneling: Your data travels through a secure “tunnel” to the VPN server, masking your IP.
- Trust model: You must trust your VPN provider with the data leaving your device, subject to their privacy policy and jurisdiction.
- Split tunneling: Some traffic goes through the VPN while other traffic goes directly to the internet—great for performance but requires careful configuration to maintain safety.
- DNS handling: A safe VPN routes DNS queries through the VPN to prevent leaks that reveal your browsing history.
Safety myths vs. realities NordVPN and IP ranges: what you need to know about your IP address and NordVPN ranges
- Myth: VPNs hide illegal activity. Reality: They can protect privacy, but illegal activity remains illegal and may still be traced through other means.
- Myth: All VPNs are safe. Reality: Safety depends on policy, leaks, and security practices; shady providers can log data or inject ads.
- Myth: VPNs make you completely anonymous. Reality: They provide privacy and security, not total anonymity; cookies, apps, and device identifiers can still reveal information.
- Myth: Free VPNs are always safe. Reality: Free services often monetize data or have weaker protections; paid, reputable services are generally safer.
- Myth: A VPN fixes poor device security. Reality: VPNs protect data in transit but don’t replace endpoint security like up‑to‑date OS, anti‑malware, and strong passwords.
Safety in real‑world scenarios
- Public Wi‑Fi at airports or cafes: A VPN adds a strong layer of protection against snooping on shared networks.
- Remote work and sensitive data: A strong VPN with business features split tunneling controls, MFA, and device management helps keep corporate data secure.
- Streaming and geo‑bypassing: VPNs can help access geo‑restricted content, but some services actively block known VPN IPs; look for providers with rotating IP pools.
- Travel and cross‑border data: A VPN can help maintain privacy and circumvent local censorship, but always review local laws and service terms.
- Mobile privacy: Ensure the VPN app has minimal permission access and uses encrypted tunnels on mobile data as well as Wi‑Fi.
Privacy and data handling: what to expect from providers
- Privacy policy clarity: Look for a plain‑language policy that states what data is collected and why.
- Data retention: Many reputable VPNs minimize or eliminate traffic logs; some maintain connection metadata for operational purposes—understand what’s stored.
- Jurisdiction considerations: Providers in privacy‑friendly regions may be compelled by law to comply with requests; some publish transparency reports.
- Advertisers and tracking: Some VPNs incorporate in‑app ads or partner with advertisers; this can impact privacy.
- Audits and certifications: Independent audits increase trust; verify the scope and date of audits.
Security features that matter
- Kill switch: Prevents data leaks if the VPN drops.
- DNS leak protection: Ensures DNS requests stay within the VPN tunnel.
- IPv6 leakage protection: Disable or tunnel IPv6 to prevent leaks in IPv6 environments.
- Multi‑hop or double VPN: Routes traffic through multiple servers for added anonymity; may reduce speed.
- Split tunneling: Lets you choose which apps go through VPN; good for performance but must be configured securely.
- Threat protection: Some VPNs include malware blocking, ad blocking, or tracker protection.
- Sturdy authentication: MFA, strong passwords, and device trust settings improve account security.
How to test a VPN for safety and leaks
- IP address check: Use online tools to confirm your real IP isn’t shown when connected to the VPN.
- DNS leak test: Check if DNS requests leak to your ISP when connected to the VPN.
- WebRTC leak test: Check for IP leaks via WebRTC in your browser.
- Kill switch test: Disconnect the VPN to ensure traffic stops immediately.
- IPv6 testing: Ensure IPv6 is either disabled or routed through the VPN.
- Speed consistency: Run speed tests with and without VPN to understand performance tradeoffs.
- Leak tests after updates: Re‑test after app updates to confirm protections remain intact.
- Independent reviews: Look for third‑party tests and community trust signals.
VPN safety for different devices and networks How to Use Hola Free VPN on Microsoft Edge for Better Browsing
- Windows/macOS: Ensure the VPN client is current, use kill switch and DNS protection, verify no leaks.
- iOS/Android: Use reputable apps, enable background protection, and manage permissions; watch for battery impact.
- Routers: Install VPN on a router for network‑wide coverage; requires more setup but protects all connected devices.
- Smart TVs and streaming devices: VPN can help with geo‑restrictions, but some devices don’t support VPN apps; use router‑level VPN or smart DNS as alternatives.
Performance vs. safety: finding the right balance
- Protocol choice: WireGuard tends to offer good speed with strong security; OpenVPN remains widely compatible.
- Server selection: Proximity reduces latency; rotating IP pools can help with streaming access.
- Hardware impact: VPNs add overhead; older devices may show slower performance; consider device capability when choosing features like multi‑hop.
- Battery life: Mobile VPN use can impact battery; adjust settings for a balance of safety and endurance.
Practical setup checklist
- Choose a reputable provider with:
- AES‑256 encryption
- No‑logs policy with independent verification
- DNS and WebRTC leak protection
- Kill switch and MFA options
- Clear privacy policy and transparent audits
- Install the official app from the provider’s site or app store.
- Configure settings:
- Turn on kill switch
- Enable DNS leak protection
- Disable IPv6 or route IPv6 through VPN
- Enable threat protection if available
- Enable split tunneling only for non‑sensitive traffic if you need it
- Verify safety:
- Run IP, DNS, and WebRTC leak tests
- Test kill switch behavior on simulated disconnects
- Daily habits:
- Keep the app updated
- Use strong, unique passwords and MFA
- Review permissions regularly
- Be mindful of incidental data leakage from apps or browser extensions
Tips for staying safe online beyond the VPN
- Use secure, updated browsers and enable standard privacy protections.
- Install reputable security software and keep it updated.
- Be cautious with public charging stations and USB devices use a USB data blocker if possible.
- Regularly review which apps have network access on your devices.
- Practice good password hygiene and consider a password manager.
- Be mindful of phishing attempts and malicious links, even inside private networks.
Data privacy considerations you should know
- Data ownership: You own your data, but the VPN provider handles your traffic after it exits the tunnel; policies vary by provider.
- Corporate VPNs: If you’re using work VPNs, your employer may have access to logs and traffic conventions; follow company policies.
- Government data requests: Some jurisdictions may compel providers to comply; independent audits help verify how data is handled.
- Logging variations: Some providers log connection metadata even if they claim not to log content; check what is retained and why.
Performance benchmarks and statistics 초보자도 쉽게 따라 하는 미꾸라지 vpn 사용법 완벽 가이 - VPNs
- Global VPN usage trends show a steady rise in demand for privacy and security tools, driven by public Wi‑Fi use, streaming, and remote work.
- Typical VPN speed impact ranges from 5% to 40% depending on protocol, server load, and distance.
- Independent audits and transparency reports have become more common, signaling higher industry standards.
- DNS and IPv6 leaks remain a notable risk point for many users; proactive configuration reduces risk.
Frequently Asked Questions
Is a VPN safe for streaming and gaming?
Yes, a VPN can improve privacy and help bypass geo‑restrictions, but some services block VPNs. Look for providers with a large number of rotating IPs and robust streaming support.
Can a VPN make me completely anonymous?
No. A VPN hides your IP and encrypts traffic, but it doesn’t make you invisible. Other identifiers and online behavior can still reveal information.
Do free VPNs exist that are safe?
Some free options exist, but they often come with trade‑offs like data limits, slower speeds, or data‑sharing policies. For serious safety, a reputable paid VPN is usually a better choice.
What should I look for in a privacy policy?
Look for explicit no‑logs commitments, what data is collected and for how long, third‑party sharing, and how data is protected and deleted. Como activar una vpn en microsoft edge guia completa y sencilla para tu navegador
How do I know if a VPN leaks my data?
Run DNS, WebRTC, and IP leak tests while connected to the VPN. If your real IP or DNS shows up, there’s a leak.
Should I use a VPN on all devices?
Yes, ideally. You’ll get the most consistent protection when all devices and networks you use route through a VPN, especially on public Wi‑Fi.
How important are independent audits?
Very important. They provide third‑party verification of the provider’s claims and help you trust the service.
Can VPNs be used on mobile data?
Yes, VPNs work on mobile data and Wi‑Fi. Some providers optimize mobile performance and battery usage.
What about malware protection with VPNs?
Some VPNs offer built‑in threat protection, but you should also use reputable security software and practice safe browsing. La vpn si disconnette spesso ecco perche succede e come risolvere definitivamente
How often should I change VPN servers?
If you’re chasing better speeds, try nearby servers or ones with lower load. For privacy, keep a routine and avoid excessive switching.
Is it legal to use a VPN everywhere?
Most places have no laws against using VPNs, but some countries restrict or ban VPN usage. Always check local laws before traveling.
Key takeaways
- A safe VPN hinges on policy transparency, strong technical controls, and independent verification.
- Expect protections like kill switches, DNS leak prevention, and secure protocols.
- Always verify your safety with independent tests and stay current with updates.
- Pair your VPN with good digital hygiene to maximize safety and privacy.
References and further reading
- Privacy and security guides from reputable tech outlets
- Independent VPN audits and transparency reports
- Network security best practices for home and office
Useful URLs and Resources Norton vpn region not working heres how to fix it fast: Fast, Friendly Guide to Get Around VPN Region Blocks
- NordVPN official page for trusted privacy features and audits - https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441
- Privacy advocates and security tutorials - https://en.wikipedia.org/wiki/Privacy
- Public Wi‑Fi safety tips - https://www.staysafeonline.org
- WebRTC leak test tool - https://www.dnsleaktest.com
- IP address check tool - https://ipleak.net
- DNS leak test tool - https://www.dnsleaktest.com
- VPN protocol comparisons - https://www.vpnmentor.com/blog/vpn-protocols-guide/
- Independent security audits overview - https://www.prnewswire.com/news-releases/security-audits
Frequently Asked Questions continued
How do I pick a VPN for a specific country or region?
Consider server coverage, privacy laws, and latency. Choose providers with servers in your target region and strong privacy commitments.
Do VPNs work on smart TVs?
Some do via apps; others require a router VPN or DNS workaround. Check device compatibility and provider instructions.
Are VPNs illegal to use at school or work?
Most places allow VPNs for personal use, but some organizations may restrict or monitor VPN traffic. Always follow local policies.
Can I use a VPN for torrenting safely?
VPNs can protect privacy and hide traffic, but legal implications vary by country and content. Use legal content and reputable, privacy‑minded providers. Protonvpn not opening heres how to fix it fast
What happens if a VPN provider is compromised?
If safety practices fail, your data could be at risk. That’s why audits, transparent policies, and strong encryption matter.
If you want a reliable, privacy‑focused VPN with a strong track record, consider checking out NordVPN via the affiliate link above, which supports safe browsing and privacy practices. Remember: the right VPN is a tool—not a magic shield—so pair it with smart online habits for real peace of mind.
Sources:
琉璃神社分享快乐:最全VPN选购与使用指南,助你安全上网、畅享无界
如何在macbook上轻松安装和使用vpn?新手指南:快速上手、常见误区与安全要点
Is nordvpn a good vpn for privacy, streaming, and security in 2026 Как скачать и установить nordvpn на пк с windows 11 по защиту онлайн: простой путеводитель по nordvpn на Windows 11
安卓 vpn:全面指南与实用选购要点,提升安全与隐私
Octohide:全面VPN指南,围绕隐私、速度与实用性的一站式解析